This error is bad news, i.e., if you don't have a recent backup. I don't know of any way to bypass this error either. Apple support said there isn't one and to just go through with the restore. What does the restore do? Running the restore will reset your iphone back to factory settings meaning just the way you had it when you bought it, opened it, then started it for the first time.
1. Run the restore
Just do it. You know, like Nike says: just do it (showing my age huh?). If you don't, you won't be able to use your iPhone. In iTunes click on the restore button and let it do the work. The restore shouldn't take longer than 10 minutes. There are progress bars through the whole thing.
2. Run your backup if you have one
iTunes will detect the restored iPhone. iTunes will also give some indication of running a backup (if you're using the "authorized" computer - the computer you have iTunes on that you use for charging and syncing your iPhone). If there is a backup detected then run it! Even if it's a few days old or more because if you don't you will be starting your iphone in factory settings mode.
How long does the restore from your backup take? It all depends on the size of your backup, i.e. how many apps you had, music, notes, etc. The restore from backup on my boss's iPhone 5 took about a hour or a little more.
3. Make sure things run correctly
I like to make sure things are running correctly before I give the device back to whomever. Make sure you can receive and send email correctly, that your iTunes store experience is correct, device to computer syncing works, iCloud syncing works and that other important apps are working.
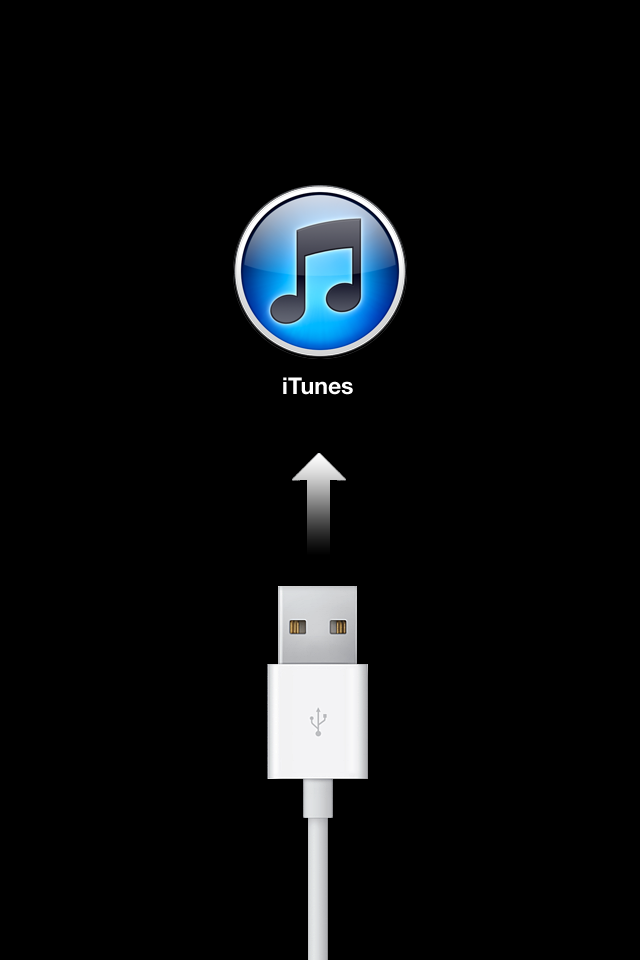
All in all, this process wasn't as *bad* as I thought it would be. Why does this error happen? My boss told me his iPhone 5 began an update and that the didn't have time for it so he unplugged his iPhone from his computer and that's when he couldn't get his iPhone past the screen with the usb cable pointing to the iTunes logo.
So, if your device (whatever it is) is in "installing an update" mode then LET IT DO IT BEFORE DISCONNECTING IT OR TURNING IT OFF.
Wednesday, January 30, 2013
Wednesday, January 23, 2013
Configure Server 2008 VPN Behind Sonicwall TZ 210
You want to use your Server 2008 as a VPN for accessing remote applications and data at your workplace instead of your VPN firewall or a router that has that option? Understandable. Exciting that you found this post huh? No? Only useful? Well, okay.
First, install the server role.
The server role isn't called 'vpn' or anything like that. Go to Start > Server Manager > Add Roles > Select Network Policy and Access Services > Next > Next.
Select Remote Access Service > Next > Install > The Service takes a long time so make a sandwich or a salad if you're a vegetarian. When it finishes, click close.
Now go to Start > Administrative tools > Routing and Remote Access > The Server will have a red "south" Arrow on it > Right Click the Server and Select "configure and enable routing and remote access"
Next > Select "Custom Configuration" > Next.
VPN Access > Next
When prompted select "Start Service" > service will start > you can now close the Routing and Remote Access Console.
Make sure the user has 'dial-in access' in Active Directory Users and Computers. For example find Joe Smith in Active Directory. Go to his properties. In the dial-in tab, click "allow access."
Now we must go to the Sonicwall device.
Since the Server 2008 box is behind our firewall we must open the correct port and protocol to Server 2008. TCP Port 1723 and GRE (Generic Routing Encapsulation) to be exact.
You will need two rules in your Sonicwall. The first one is NAT.
Source original - any
Source translated - original
Dest original - your public IP
Dest Translated - your vpn server internal IP
Service original - pptp
service tranlated - original
The second rule is a firewall rule.
Wan to Lan
Source - any
Destination - my external IP
Service - pptp
Action - allow
These two rules cover the TCP port 1723 and the GRE protocol requirements.
Now you need to connect your remote client to the VPN server (your server 2008 box).
The following is for Windows Vista and Windows 7 machines.
Click on Start > Control Panel > Network and sharing Center > Connect to a Network > Set up a Connection or Network > Connect To a Workplace > Next.
Use My Internet Connection (VPN) > Enter the public IP address of the VPN server > Enter a Name for the Connection > Next > Enter your Domain Logon details > Connect.
I hope this helps. I couldn't find a single post covering all of this. There might be one out there. I couldn't find one so that's why I wrote this post. Enjoy!
First, install the server role.
The server role isn't called 'vpn' or anything like that. Go to Start > Server Manager > Add Roles > Select Network Policy and Access Services > Next > Next.
Select Remote Access Service > Next > Install > The Service takes a long time so make a sandwich or a salad if you're a vegetarian. When it finishes, click close.
Now go to Start > Administrative tools > Routing and Remote Access > The Server will have a red "south" Arrow on it > Right Click the Server and Select "configure and enable routing and remote access"
Next > Select "Custom Configuration" > Next.
VPN Access > Next
When prompted select "Start Service" > service will start > you can now close the Routing and Remote Access Console.
Make sure the user has 'dial-in access' in Active Directory Users and Computers. For example find Joe Smith in Active Directory. Go to his properties. In the dial-in tab, click "allow access."
Now we must go to the Sonicwall device.
Since the Server 2008 box is behind our firewall we must open the correct port and protocol to Server 2008. TCP Port 1723 and GRE (Generic Routing Encapsulation) to be exact.
You will need two rules in your Sonicwall. The first one is NAT.
Source original - any
Source translated - original
Dest original - your public IP
Dest Translated - your vpn server internal IP
Service original - pptp
service tranlated - original
The second rule is a firewall rule.
Wan to Lan
Source - any
Destination - my external IP
Service - pptp
Action - allow
These two rules cover the TCP port 1723 and the GRE protocol requirements.
Now you need to connect your remote client to the VPN server (your server 2008 box).
The following is for Windows Vista and Windows 7 machines.
Click on Start > Control Panel > Network and sharing Center > Connect to a Network > Set up a Connection or Network > Connect To a Workplace > Next.
Use My Internet Connection (VPN) > Enter the public IP address of the VPN server > Enter a Name for the Connection > Next > Enter your Domain Logon details > Connect.
I hope this helps. I couldn't find a single post covering all of this. There might be one out there. I couldn't find one so that's why I wrote this post. Enjoy!
Application Authentication Through VPN Tunnel Problem
This is a good "from the trenches" story, especially if you like networking. I've been working on this problem for exactly a week (no, not a crazy long time, but still, it's a while) and today I finally fixed the issue.
At work our main application for hr, payroll, general ledger, and employee self-service is called Springbrook. It's a nice, though slightly bloated, application that works for us. It's important to know how Springbrook is used for this story to make sense. Please bear with me while I give you the rundown.
The Springbrook application is installed on server1 along with the programs OpenEdge and Progress to handle all of the data processing for Springbrook. We have a separate drive just for Springbrook, OpenEdge and Progress. When the app is executed, the login page is opened in Internet Explorer. Springbrook uses the LDAP protocol (in our case Active Directory) to authenticate the user trying to login against the login id’s already inside of Springbrook, so when the session is established it requires that the user logs in and is authenticated to the domain which in turn makes the connection to the LDAP connector which verifies user info and allows them access.
How do the users run Springbrook? I have setup a mapped drive to the server on their workstations. I setup a desktop shortcut to the executable so the employees don't have to go that mapped drive each time and double-click the executable. So, it looks and feels like Springbrook is installed locally on their workstations.
This setup works great for local users right? What about remote users? We have those. One currently, but we're about to have one more permanent remote user. I decided to go with the VPN option in our Sonicwall TZ 210. It worked great. It was fast, surprisingly, and the user didn't have to go through remote desktop to use Springbrook which was nice. I mapped a drive to the server so she was able to use it just like the local users do. Fantastic.
Well, eight days ago Springbrook ran a service pack for the application. No problem because they do that on occasion to correct problems in the modules. The next day my remote user couldn't use Springbrook. I asked her if the VPN connected fine and she said "yeah, I can connect to the network, but I can't login to Springbrook." I told her to wait and I would be there in about fifteen minutes. I went through the checklist and found that nothing should be preventing her from logging in to Springbrook. I was so confused. The only change was the service pack install. I contacted Springbrook about this and the tech told me that somehow the authentication isn't happening in the VPN tunnel.
Okay. I knew that, haha
He then said that they use Citrix for their remote employees. I'm sure Citrix has a very nice WebApp tool, but if I can do this through a VPN tunnel and save us money that would be great. I don't like to go with paid solutions if we can implement a solution with equipment and software we already have. So, since I couldn't figure the problem out I decided to hit the forums. A person at serverfault recommended the VPN option in Windows Server 2008. I thought, "Why not?" I set that up in my lab. The VPN connection was fast, smooth, and near painless. *I'm going to write a blog post about it because it's so simple and there wasn't a single post containing all of the steps, instead I had to piece it together from multiple posts - ugh* Anyway, I connected to the VPN server, accessed the Springbrook share, ran Springbrook and guess what? I couldn't login to Springbrook. THE EXACT SAME PROBLEM. I understood possibly having an authentication issue using Sonicwall's VPN but there is no way that my server couldn't authenticate me because I connected to that server with my Active Directory credentials.
I was livid. Suddenly, I thought, "Why don't I try adding the .local to the domain name in the domain field?" The Springbrook login window requires a username, password, and a domain. All users and I mean all of our users don't have to put the .local for the domain however when you're up against a wall you try anything. I added .local to the domain name and then Springbrook launched. That fixed the issue. I couldn't believe it. I then wondered if that was the problem going through Sonicwall? I called the remote user, asked her when I could work on this for her, she said now and so I went to her office. I enabled the Sonicwall VPN connection, ran the Springbrook application, added the .local to the domain name and like a charm I was running Springbrook. The user was happy and yeah I was happy, but I want to know why I have to add .local to the domain name when logging in remotely now. Remote users didn't have to do that before last week. Why now?
I'm not satisfied. Could it be the recent Springbrook service pack update? I contacted Springbrook support and hopefully I'll hear back from them soon.
Anyway, lesson is try the easy things first. Like usual.
At work our main application for hr, payroll, general ledger, and employee self-service is called Springbrook. It's a nice, though slightly bloated, application that works for us. It's important to know how Springbrook is used for this story to make sense. Please bear with me while I give you the rundown.
The Springbrook application is installed on server1 along with the programs OpenEdge and Progress to handle all of the data processing for Springbrook. We have a separate drive just for Springbrook, OpenEdge and Progress. When the app is executed, the login page is opened in Internet Explorer. Springbrook uses the LDAP protocol (in our case Active Directory) to authenticate the user trying to login against the login id’s already inside of Springbrook, so when the session is established it requires that the user logs in and is authenticated to the domain which in turn makes the connection to the LDAP connector which verifies user info and allows them access.
How do the users run Springbrook? I have setup a mapped drive to the server on their workstations. I setup a desktop shortcut to the executable so the employees don't have to go that mapped drive each time and double-click the executable. So, it looks and feels like Springbrook is installed locally on their workstations.
This setup works great for local users right? What about remote users? We have those. One currently, but we're about to have one more permanent remote user. I decided to go with the VPN option in our Sonicwall TZ 210. It worked great. It was fast, surprisingly, and the user didn't have to go through remote desktop to use Springbrook which was nice. I mapped a drive to the server so she was able to use it just like the local users do. Fantastic.
Well, eight days ago Springbrook ran a service pack for the application. No problem because they do that on occasion to correct problems in the modules. The next day my remote user couldn't use Springbrook. I asked her if the VPN connected fine and she said "yeah, I can connect to the network, but I can't login to Springbrook." I told her to wait and I would be there in about fifteen minutes. I went through the checklist and found that nothing should be preventing her from logging in to Springbrook. I was so confused. The only change was the service pack install. I contacted Springbrook about this and the tech told me that somehow the authentication isn't happening in the VPN tunnel.
Okay. I knew that, haha
He then said that they use Citrix for their remote employees. I'm sure Citrix has a very nice WebApp tool, but if I can do this through a VPN tunnel and save us money that would be great. I don't like to go with paid solutions if we can implement a solution with equipment and software we already have. So, since I couldn't figure the problem out I decided to hit the forums. A person at serverfault recommended the VPN option in Windows Server 2008. I thought, "Why not?" I set that up in my lab. The VPN connection was fast, smooth, and near painless. *I'm going to write a blog post about it because it's so simple and there wasn't a single post containing all of the steps, instead I had to piece it together from multiple posts - ugh* Anyway, I connected to the VPN server, accessed the Springbrook share, ran Springbrook and guess what? I couldn't login to Springbrook. THE EXACT SAME PROBLEM. I understood possibly having an authentication issue using Sonicwall's VPN but there is no way that my server couldn't authenticate me because I connected to that server with my Active Directory credentials.
I was livid. Suddenly, I thought, "Why don't I try adding the .local to the domain name in the domain field?" The Springbrook login window requires a username, password, and a domain. All users and I mean all of our users don't have to put the .local for the domain however when you're up against a wall you try anything. I added .local to the domain name and then Springbrook launched. That fixed the issue. I couldn't believe it. I then wondered if that was the problem going through Sonicwall? I called the remote user, asked her when I could work on this for her, she said now and so I went to her office. I enabled the Sonicwall VPN connection, ran the Springbrook application, added the .local to the domain name and like a charm I was running Springbrook. The user was happy and yeah I was happy, but I want to know why I have to add .local to the domain name when logging in remotely now. Remote users didn't have to do that before last week. Why now?
I'm not satisfied. Could it be the recent Springbrook service pack update? I contacted Springbrook support and hopefully I'll hear back from them soon.
Anyway, lesson is try the easy things first. Like usual.
Thursday, January 10, 2013
malware removal and prevention like a boss
It's highly likely that malware will never go away, no matter how awesome computers and the internet become malware will most likely still hang around like that old suit or old dress your parents never remove from their wardrobe and wear to parties. Gross. Anyway, since malware is here to stay, how does one go about removing it? Better, how does one prevent it? It can happen.
Check out this new blog post at InfoWorld written by Roger Grimes; let him tell you how the pros remove malware. It's a good piece.
While you're here let me give some advice on prevention. While malware is here to stay, it doesn't have to come stay at your house. This prevention method is near perfect.
1. Get behind a router/hardware firewall
If you have a direct line to the internet then you're screwed. You need to be behind a firewall and not just a firewall, but a hardware firewall. This is a good one. It's affordable and it rocks.
2. Antivirus
You know, I think if you're behind a firewall and you practice safe browsing then you're most likely good to go. However, many people don't practice safe browsing. So, download and install Microsoft Security Essentials. It's the best antivirus out there in my opinion. Note: if you're running windows 8 then you don't have to do this because it's already installed and running on your system.
3. Safe-Browsing Add-on
This handy tool from Web of Trust rates websites for you and will give you a warning screen upon clicking a poorly rated link. This helps out a lot because it trains the user in safe browsing. Get it here. You will need to install it on every browser you use.
4. OpenDNS
This is, arguably, optional. Using OpenDNS will not only improve your DNS performance (which makes your internet browsing faster), but it also has excellent security tools like malware prevention and safe browsing. The web filter is not only good for preventing porn, but it also filters sites that are infested with malware and other junk. Good stuff. Use it.
So those are four ways to prevent your pc and network from malware infections. However, these tools can't keep you (totally keep you) from user installed malware. So, learn about safe browsing.
Check out this new blog post at InfoWorld written by Roger Grimes; let him tell you how the pros remove malware. It's a good piece.
While you're here let me give some advice on prevention. While malware is here to stay, it doesn't have to come stay at your house. This prevention method is near perfect.
1. Get behind a router/hardware firewall
If you have a direct line to the internet then you're screwed. You need to be behind a firewall and not just a firewall, but a hardware firewall. This is a good one. It's affordable and it rocks.
2. Antivirus
You know, I think if you're behind a firewall and you practice safe browsing then you're most likely good to go. However, many people don't practice safe browsing. So, download and install Microsoft Security Essentials. It's the best antivirus out there in my opinion. Note: if you're running windows 8 then you don't have to do this because it's already installed and running on your system.
3. Safe-Browsing Add-on
This handy tool from Web of Trust rates websites for you and will give you a warning screen upon clicking a poorly rated link. This helps out a lot because it trains the user in safe browsing. Get it here. You will need to install it on every browser you use.
4. OpenDNS
This is, arguably, optional. Using OpenDNS will not only improve your DNS performance (which makes your internet browsing faster), but it also has excellent security tools like malware prevention and safe browsing. The web filter is not only good for preventing porn, but it also filters sites that are infested with malware and other junk. Good stuff. Use it.
So those are four ways to prevent your pc and network from malware infections. However, these tools can't keep you (totally keep you) from user installed malware. So, learn about safe browsing.
Monday, January 7, 2013
10 Essentials Skills for Hyper-V 3.0
If you're interested learning 10 skills for using the next generation of hyper-v, I highly recommend this webinar by Brien Posey from Veeam.
Subscribe to:
Comments (Atom)